The mining industry’s growing appetite for real-time data collection and analysis brings with it an equally robust need for wider use of mobile devices and broader sensor networks – all of which can also heighten an operation’s vulnerability to cyberattacks when its data security and management practices can’t meet the challenge.
Working smarter and safer has become an industry creed for employee welfare. Companies should apply the same principles to data management.
By Russell A. Carter, Contributing Editor
“Data” might be the most imprecise word in the language of business, both in terms of meaning and value. For mineral producers, a data item could be anything from a momentary, routine signal from a remote sensor, to a single cell in a vast financial spreadsheet. As for value, how is it measured? Is a gigabyte of drill hole data worth more than a gigabyte sent from a pipeline pressure sensor?
Sometimes the actual value of data can only be determined when it’s misused or missing. The cost of ignoring or misinterpreting data from a haul truck temperature sensor might be reflected in the price of an engine overhaul, and the eventual financial impact ensuing from theft of sensitive spreadsheet information could provide a quick indication of how much that data was worth — both to the company that owned it and the hacker who stole it.
One indication of how valuable a company’s data can be was presented in a recent article on the Forbes.com website that pointed out that several large companies in other industrial sectors (airlines, retail, etc.), stressed by pandemic-related economic factors, had certain data assets appraised in order to qualify these assets as collateral to secure large business loans. The appraisal results, according to the article, suggested the value of the data was two to three times more than the actual market value of the companies themselves.
Data management and data security can be viewed as two sides of the same coin. Data that isn’t well-managed probably isn’t secure, and security measures won’t be optimally effective without prior determination of which types of business data are most valuable and potentially vulnerable. Management and security practices covering the full range of mining activity from exploration to port delivery need to be capable of protecting vital information from misuse, theft and corruption, because the threat level to the mining industry is growing.
IBM’s Security business group released a study of the financial impact of data breaches on organizations that showed the cost of these incidents has risen 12% over the past five years to $3.92 million each on average. The rising costs, according to IBM, are representative of the multiyear financial impact of breaches, increased regulation and the complex process of resolving criminal attacks. And, breach costs aren’t short-lived: For the first time, the report examined the long-term financial impact, finding that the effects of a data breach are felt for years. While an average of 67% of data breach costs were realized within the first year, 22% accrued in the second year and another 11% accumulated more than two years after a breach.
Given the scope of possible consequences caused by cyber intrusion, the mining industry has flashed mixed signals in response; showing signs of casualness about the matter in some cases, while in other instances, it has moved forward positively to meet the challenges. Two examples:
The Australian survey organization State of Play, after interviewing and analyzing information from several large Australian mining and service companies, remarked that comments from high-level mining executives indicated that 98% of them expected a catastrophic event would be necessary to drive an industry response to cybersecurity, at least in that country.
In contrast, following the 2017 Prospectors and Developers Association of Canada (PDAC) trade show, six mining companies formed a group focused on the cybersecurity needs of the mining industry. The Mining and Metals Information Sharing and Analysis Center (MM-ISAC), as it is known, was established to protect members against incidents that could impact safety, environmental sustainability or operational productivity by sharing threat and vulnerability information, managing industry contingency planning, and providing opportunities for training security staff and incident response teams.
New solutions to maximize the usefulness – and thus the value – of data are being offered to producers at a steady clip. The key to maximum effectiveness is to find the solution that fits the user’s specific needs and resources for data utilization, storage and management.
Moving Beyond Legacy Limits
In a recent blog post on the State of Play website, an organization spokesperson explained that the industry’s dependence on legacy systems, coupled with disinclination to adopt new software platforms, is further complicated by exponential growth in connected devices on mining networks due to investments in automation and monitoring technologies.
These legacy systems are often Industrial Control Systems (ICS), comprising the SCADAs, DCSs and PLCs that control process equipment. ICSs, in general, were never intended or designed to be connected to other systems, but with the advent of industry digitalization and the growth of IIoT applications, now they are — not just to other ICSs, but to company-wide communications systems and other platforms, thus expanding potential avenues for intrusion.
Apala Ray, global cybersecurity manager, Industrial Automation, Process Industries at ABB, told E&MJ that as recently as a decade ago, cyberattacks targeting industrial control systems were rarely heard of. The emergence of Stuxnet, the first computer malware to tar-
get control systems found in industrial plants, and its role in the now-infamous attack on nuclear infrastructure in Iran in 2010 — followed by two high-profile attacks on a German steel mill and Ukraine’s power grid — changed all that.
“Stuxnet was a wake-up call that operational technology (OT) and not just information technology (IT) could be targeted by cyberattacks, as well as ransomware like WannaCry and NotPetya, not targeted for OT can create huge impact,” Ray said. “The estimated recovery cost from the 2017 NotPetya ransomware attack to Maersk, for example, may run to $300 million.
“In the past, many industrial operators, including those in the mining sector, believed that because their OT and IT systems were not connected, they were not vulnerable. With digital and automation solutions now offering increased visualization and interconnectedness, this is no longer the case.”
Mining cyberattacks typically take the form of espionage campaigns that target intellectual property and proprietary information, or phishing, whereby a user is tricked into divulging confidential data. Studies by US Homeland Security show that such attacks can be mitigated by up to 98% if industrial operators have put basic digital hygiene and process controls in place.
These fundamental safeguards constitute the first stage in ABB’s three-layered approach to cybersecurity. “Our advice to clients is to make sure they apply the latest updated security patches and anti-virus definition procedures,” Ray explained. “Use the concept of network segmentation and make sure you have a clearly defined back-up and recovery process in place. The latter is crucial in allowing a mine, for example, to continue to operate and avoid costly production downtime following a cyberattack.
“It is also important to have password policies and an asset inventory. These may be basic processes and controls, but they can eliminate most of the attacks on industrial automation control systems.
“Cybersecurity is a balance between risk, usability and cost. Our second layer of protection involves providing services to our clients, and the third encompasses a more mature OT monitoring solution.”
ABB’s Cyber Security Fingerprint service, for example, identifies critical control system vulnerabilities at mining facilities by focusing on three areas: procedures and protocols; group security policies; and server and workstation settings. The solution combines information from an ABB control system along with insights gained from interviews with working personnel.
“It is important to remember that cybersecurity is not a standalone solution: it is about people, processes and technology,” said Ray. “We recently worked at a mine in Sweden that had employed ABB’s Control System, called ABB Ability System 800xA, in the processing plant for some time. Using the ABB Ability Cyber Security Fingerprint the mine’s cybersecurity policies and how they are implemented day by day were assessed.”
The solution generates a detailed report on gaps in the enterprise’s existing cybersecurity measures and uses an analytics tool to compare the results with recognized industry standards.
“Having then assessed whether the correct procedures and policies are in place, the Cyber Security Fingerprint tool finally produces a report that contains detailed recommendations on how the client can reduce vulnerabilities, and implement a focused and sustainable security strategy,” explained Ray.
However, outdated or poorly managed enterprise resource planning (ERP) systems also carry additional risk factors.
Deloitte noted in its Tech Trends 2019 report, “Core modernization seeks to solve the riddle of how companies with significant investments in legacy systems can extract more value from these systems by making them a foundation for new disruptive innovations. As major ERP providers roll out next-generation platforms designed to enable real-time transactional processing and data analysis,” the report’s authors wrote, “mining companies are facing an imminent need to update their ERP systems and make choices on whether to host their data on premises or in the cloud.”
Whether pursuing enterprise-wide transformation or making incremental improvements, mining companies need to consider the “five R’s” when contemplating core modernization, according to Deloitte:
Replatform – Upgrade platforms through technical upgrades, software updates, and migration to modern operating environments (such as cloud platforms, in-memory databases, and virtualized environments).
Revitalize – Layer on new capabilities to enhance stable underlying core processes and data. This could include enhancing usability with digital solutions that improve employee engagement, adopting visualization suites to fuel data analysis, or introducing cognitive techniques to strengthen reporting and support predictive and prescriptive analytics.
Remediate – Address internal complexities of existing core implementations. This could involve reconciling master data to simplify business processes and introduce single views of key data, integrating disparate systems to streamline data sharing with external partners, or rationalizing custom extensions and bespoke solutions to simplify system maintenance.
Replace – Introduce new systems for parts of the core. This may mean adopting new products from existing vendors or revisiting build vs. buy decisions as new entrants roll out new solutions. Ideally, organizations will use these pivots to revisit their needs and build new capabilities rather than replicating the work habits associated with their old systems.
Retrench – Do nothing, which can be strategic as long as it’s an intentional choice.
The State of Play blog also predicted that “things will get worse” until appropriate security processes and protocols are put in place. Things actually have gotten worse – the COVID-19 pandemic has added complexity to an already daunting technological puzzle by forcing companies to expand remote-worker assignments for health and safety reasons. As explained by Microsoft’s Threat Protection group, “The increasing pervasiveness of cloud services in today’s work environments, accelerated by a crisis that forced companies around the globe to shift to remote work, is significantly changing how defenders must monitor and protect organizations. Corporate data is spread across multiple applications — on-premises and in the cloud — and accessed by users from anywhere using any device. With traditional surfaces expanding and network perimeters disappearing, novel attack scenarios and techniques are introduced.”
A sobering assessment of the elevated risk of data loss or corruption from work-at-home or other remote locations was provided recently in a report from data security company Tessian. The report, titled The State of Data Loss Prevention 2020, notes that despite a high level of confidence expressed by corporate IT leaders — 91% say they trust their employees to follow security best practice while out of the office — nearly half (48%) of employees admit they’re less likely to.
Tessian said its latest research shows these key findings:
• 50% of employees say they’re less likely to follow safe data practices when working from home because they’re not working on their usual devices.
• 48% of employees say they’re less likely to follow safe data practices when working from home because they feel as though they’re not being watched by their IT teams.
• 47% of employees say they’re less likely to follow safe data practices when working from home because they’re distracted.
In the same vein, writing for the Global Mining Guidelines Group – a Quebec-based organization promoting collaboration and innovation across the mining sector – Sherry Jacobs, senior manager at Accenture Security – Resource (Energy), listed several important issues that companies need to consider when responding to cybersecurity threats posed by the pandemic:
• The pandemic has created social engineering opportunities, including phishing campaigns; phishing awareness is key, as cyberespionage and cybercriminal groups will take advantage of this condition while it remains active.
• Business Continuity Plans (BCPs), travel restrictions and remote work policies challenge enterprise monitoring, especially for companies that have not previously executed BCPs. Companies should advise work-from-home employees on home-based router and IoT protection and VPN best practices.
• Companies need advice on how to stratify, prioritize and outsource information security operations, and manage infrastructure and operational maintenance and growth. In-house security groups may be subject to increased demand to maintain or increase coverage under tighter budgetary constraints.
• Companies should be prepared to execute months long BCPs, including information security monitoring and response, while operating under quarantine conditions.
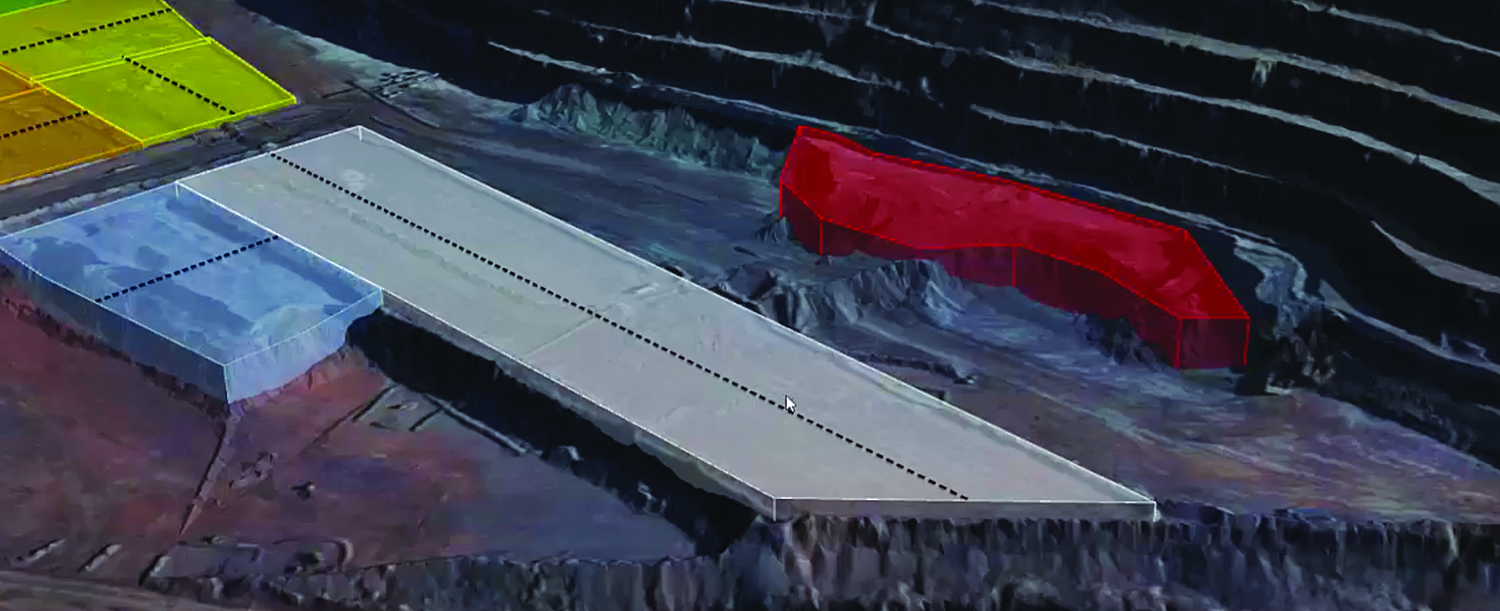
Modular Mining’s recently released Application Programming Interface (API) is intended to enable enhanced integration and increased openness through bidirectional data sharing among third-party technologies, such as RPM Global’s XECUTE planning software (shown here), and elements of Modular’s IntelliMine portfolio.
New Problems, New Solutions
The “new normal” — the anticipated industry transformation of technologies, workflows and processes powered by digitalization and boosted into overdrive by pandemic-related business concerns – will depend on large-volume data capture from an ever-expanding universe of sources. One estimate predicts the number of IoT connections to rise to 83 billion by 2024, with the industrial sector accounting for around 70% of those connections. In addition to the expansion of IoT/IIoT connections, vendors are increasingly collaborating to improve software connections via interactive data sharing between various products and platforms. For example:
RPMGlobal and Modular Mining recently extended a partnership agreement to deliver a new industry standard Application Program Interface (API) that will allow enhanced interaction between the companies’ products – in this case, RPM Global’s XECUTE ultra short-term mining planning software and Modular’s ProVision High-Precision Machine Guidance system. The API is a critical part of a solution which allows information to automatically flow between systems. The new industry standard allows applications and systems to communicate using a language that is universally understandable.
RPMGlobal chief technology officer Paul Beesley explained how the process will work: “The short-term plan, including the dig polygons, is published from XECUTE to ProVision. Then equipment status and bucket positions are sent back to the planning tool to ensure the plan is being executed. Those bucket positions can then also be used to automatically update the face positions and the schedule.”
Meanwhile, Symboticware and Uptake announced a partnership to provide mining companies with an integrated AI and data science tool to increase the productivity of mobile mining equipment. Symboticware specializes in real-time data management solutions, and Uptake is an industrial AI developer. The joint solution combines Symboticware’s SymBot onboard device, which provides comprehensive data capture from mining fleets, with Uptake’s Asset IO Asset Performance Management (APM) to apply AI to harvest predictive insights from data. Among the benefits attributed to the combination of these two products is greater visibility into assets, offering an ability to collect data from sensors, store time-stamped values in an internal database and seamlessly transmit data for AI analysis.
More recently, Uptake and conveyor-products supplier Flexco announced that they had formed a partnership to launch Flexco Elevate Belt Conveyor Intelligence, a real-time belt cleaner monitoring system that uses predictive data analytics to optimize belt conveyor productivity. Flexco said Elevate allows for the remote monitoring of belt cleaners via a wireless platform.
According to Flexco, the solution requires installation of a device to the end of each Flexco belt cleaner. Analytics are immediately aggregated and processed by Uptake. The information is then wirelessly transferred to the Flexco Elevate Dashboard.
On a broader scale, vendors in virtually every sector of digital technology are introducing new concepts and updated features on an almost weekly basis. The challenge for producers is to find the right combination of products, services and support to fit their specific new-normal business plans and environments. Here are a few examples of what’s recently become available, starting with basics such a new device access security platform, and extending along the full spectrum of industry activity from exploration to tailings storage.
Device Access Control
Xage Security, a US company that provides blockchain-protected cybersecurity solutions for industrial operations, recently introduced a universal Multiple-Factor Authentication (MFA) offering intended to enable industrial organizations to protect a variety of assets, even those that lack basic device password protection. Built to support OT/IoT use cases, Xage’s MFA solution is claimed to eliminate operational dependencies to ensure that industries can protect their assets from attacks, including the growing wave of cyberattacks that exploit remote access vulnerabilities.
The company points out that many industrial operations include machines with no password protection, or basic lock/unlock features that lack secure
access control. In the last two years alone, digital attacks targeting industrial control systems (ICS) and operational technology increased by over 2,000%. Xage says its solution enables MFA for any device and application, so companies can enforce authentication with multiple factors (passwords, one-time token, biometric, etc.) across their entire system. Operators can add MFA to all of their assets and enforce universal multifactor, identity-based, low-latency access on remote assets, even over intermittent networks.
According to Xage, authentication and enforcement are delivered at the edge and continue to operate even if connectivity to the center is lost — ensuring universal tamperproofing without additional dependencies. As a result, Xage’s MFA solution is said to capable of mitigating many common cyberattacks, including password spraying attacks, password or identity theft and phishing to plant malware on target devices.
Drill Data in the Cloud
Recognizing that COVID-19 prevention measures can disrupt conventional geotechnical studies and exploration drilling activity, several software developers in this sector announced accelerated development and other changes to their cloud-based solutions in an effort to offer smarter, more efficient data management in the current business environment.
Geoscience software company Seequent said it is speeding-up development of its cloud-based solution Seequent Central, aimed at enabling organizations to continue work on critical, large-scale projects in the COVID-19 impacted environment.
The company said Central works alongside Seequent’s other geoscience analysis, modelling and collaborative technologies to contribute understanding to subsurface geoscience and engineering design solutions. The cloud-based solution allows users in any location to visualize, track and manage geological models created for infrastructure and critical services projects, in a centralized, auditable environment. Users can readily access up-to-date information to manage risk and make better environmental and investment decisions.
Seequent said one early adopter of the platform, a Canadian junior focused on silver production in Mexico, is using its products effectively. The company, First Majestic Silver, owns and operates the San Dimas, Santa Elena and La Encantada mines and is pursuing development of its existing mineral property assets.
Seequent said First Majestic uses its Leapfrog Geo to develop a realistic presentation of the geology at each site (complex silver deposits with multiple veins), and Leapfrog Edge to aid resource estimation – and when geologic models are changed resource estimates also change dynamically. Seequent Central allows the company to publish models and resource estimates that are immediately available in real time.
IMDEX, a Western Australia-based mining technology company, recently pointed out that drilling contractors and resource companies impacted by COVID-19 restrictions can continue to operate by using cloud-connected sensors that deliver and analyze critical data. Despite restrictions disrupting travel and work, IMDEX said clients can still make time-critical decisions backed by accurate data presented in real time.
The company reported that a majority of its clients intend to keep operating while working within government-imposed restrictions and with the priority of keeping their workers safe. IMDEX said existing clients already have access to IMDEXHUB-IQ, a secure, cloud-based portal for validating field data transmitted from drill rigs, and recommended that clients use the current environment to access, review and analyze data by using IMDEXHUB-IQ to achieve efficient drillhole and sample data management from daily reporting and QA requirements to structural logging, survey and geochemical analysis.
IMDEXHUB-IQ Global Product Manager Tara Bennett-Connell said that while IMDEX HUB-IQ was available free to clients already using IMDEX tools, some were still opting to transfer data via email and USBs. “More secure, efficient and reliable methods are available, and when you can’t get access to the data through those old methods, it’s time to it’s time to change,” she noted.
IMDEX said its system has been certified for ISO/IEC 27001:2013, an international information security standard recognized in 161 countries.
Managing and Monitoring TSFs
Inmarsat, a provider of satellite-enabled managed connectivity services for land-based organizations, is now offering two versions of a Software-as-a-Service (SaaS) solution for mining companies, aimed primarily at operators that currently have tailings storage facilities (TSFs) where connectivity infrastructure and instrumentation is in place, but lack a critical component required for compliance.
The first of its two offerings, Tailings Insight Cloud, is a SaaS application claimed to be designed for interoperability, easy integration and compatibility with many sensors and IoT devices that make it capable of compiling tailings data from a broad array of sources. That data is then made visible via a single dashboard view in real time, accessible from anywhere. It also provides various ways of visualizing sensor data, while advanced alarm functionality helps notify key stakeholders of important changes in real time.
The system keeps users informed of sensor health via regular reporting, while also offering a full audit log, historical data comparison and journaling capabilities, plus it enables operators to standardize their tailings management globally, regardless of sensor type and other instrumentation.
Tailings Insight Plus, built around the cloud application core, is Inmarsat’s fully managed service. As part of the solution, Inmarsat provides global satellite connectivity, sensor integration, edge connectivity in form of LoRaWAN — a point-to-multipoint networking protocol — as well as ongoing service monitoring and management. It monitors and manages all of the infrastructure (aside from the client’s sensors) on an ongoing, end-to-end basis, with a service level agreement (SLA) tailored to client data collection needs.
Mapping the Path
As technology continues to make it progressively easier for mining companies to collect and transfer vast volumes of data, the probability of extracting greater value from that data will be matched by the likelihood that it could put an enterprise at greater risk when misused, corrupted or stolen. Companies that plan to map their own routes to cybersecurity will be looking for guidelines; here’s a set of recommendations from Accenture, a professional services company, aimed at helping organizations become “cyber resilient” to manage complex risk decisions.
Update organizational threat models. Make it a point to revisit what’s important in the organization by understanding what assets are required to deliver the business outcome, the relevant threats and vulnerabilities for the industry and regions, and what security controls are in place.
Build a strong foundation. Gain visibility over IT and OT systems/assets, understand their criticality, and recognize threats the company may be exposed to. Identify high-value assets and harden them. Prioritize legacy systems. Prepare for the worst.
Pressure test resilience like an attacker. Enhance both red attack and blue defense teams with player-coaches that use threat intelligence and communicate closely to provide analysis on where improvements need to be made.
Employ breakthrough technologies. Automate defenses. Use automated orchestration capabilities and advanced behavioral analytics.
Be proactive, go threat hunting. Develop strategic and tactical threat intelligence. Monitor for anomalous and suspicious activity. Consolidate all threat information in the organization, then develop the support structures to effectively manage it.